Posts Tagged ‘cybersecurity’
continue reading
It’s the Passwords, Stupid
During Bill Clinton’s 1992 presidential campaign, attempting to keep messages laser-focused on the recession, strategist James Carville famously quipped, “It’s the economy, stupid.” The focus worked and Clinton unseated George H.W. Bush to become the 42nd President of the United States. While much current cybersecurity talk discusses paradigm shifts such as Zero Trust and other important topics, organizations ignore the simplest protections at their peril. Password vulnerabilities still represent the most common attack vector for hackers. This article describes the scary situation regarding password vulnerabilities, defines the five most common password attack methods, and identifies best practices for protecting both individuals and businesses from these threats.
continue reading
continue reading
For a long time, Starbucks has called itself the ‘Third Place,’ which they defined as the place between home and work.
And while it could be a great place for a cup of coffee or to work outside the office, the truth is if you or your employees ever work from anywhere but the office, they may be exposing your entire business to danger.
Public networks like those at coffee shops and hotels are virtual playgrounds for hackers and cybercriminals. They love to hang out on these ‘open networks’ and attack people who use them by stealing data, passwords and even bypassing normal security to easily install malware.
Others go so far as to create ‘evil-twin’ public networks that others join by calling it something like “hotel guest” and wait for unsuspecting businesspeople to log on so they can hijack their computer.
It doesn’t end there.
continue reading
Happy 2022! The start of a new year is the perfect time for business leaders to re-evaluate their current strategies, particularly those centered around technology. The cybersecurity landscape has changed drastically since the onset of the pandemic, and new threats call for innovative solutions.
Today, I thought I’d give you an overview of a cybersecurity strategy that is gaining popularity rapidly. It’s called Zero Trust. In essence, the Zero Trust initiative uses multiple layers of security in order to protect the assets inside your network.
You may think you’re already using multiple layers of security—and you’d be right. Your smart router, antivirus solution, email spam filter, employee cybersecurity training, and more are all working overtime to keep your data safe. However, Zero Trust adds even more checkpoints into your network.
continue reading
Information Security is a constant battle. 2020 saw a huge rise in identity theft, IRS fraud, ransomware attacks both private and public, email compromise, public breaches… the list goes on. Every piece of our daily lives can be subject to these breaches, hacks, or incidents at a moment’s notice.
Sounds pretty exhausting, right? Overwhelming? Sure! But protecting yourself is easier than you think.
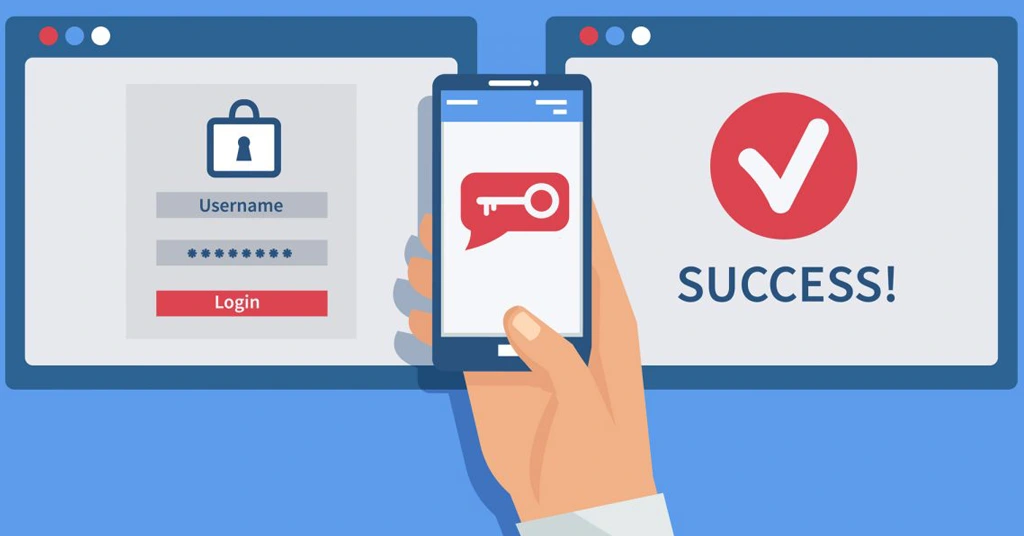
What can the average user or employee do to in this constantly changing battle? The answer is elegantly simple: Multi Factor Authentication (MFA) reduces breaches and security incidents by almost 99%.
continue reading